Service Target URLs (STUs)
What is a Service Target URL?
A Service Target URL is a hyperlink directly to the Glance service for a task. For example, when a Glance user visits this Service Target URL, they immediately see the page where they can enter a session code from a customer and join a session. (If the user is not yet logged in to Glance, they are prompted to log in first.)
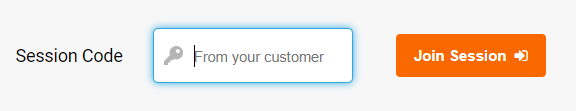
https://www.glance.net/agentjoin/agentjoin.aspx
When you set up Glance for your users, you can embed STUs in the web portal or application they use. That gives them a quick and painless way to do what they need to do with Glance.
For example, this HTML code
<a href="https://www.glance.net/agentjoin/agentjoin.aspx">Join a Glance Session</a>
produces a hyperlink like this Join a Glance Session to give direct access to a session.
Glance offers a variety of STUs for different tasks.
STUs without single sign-on
https://www.glance.net/agentjoin/AgentJoin.aspxprompts for a session key.https://www.glance.net/agentjoin/AgentView.aspx?SessionKey=kkkkis useful when you already know the session key. It joins the session directly. When using this STU the actual session key goes in place ofkkkk.
Parameters to the AgentJoin and AgentView STUs
You can add these parameters to either the AgentJoin or AgentView STUs to give the identity of the Glance user. Glance shows this identity, when it's available, to the visitor (the person using Glance to ask for help) as the session starts.
name=User+Namegives the user's personal name. As a courtesy to the person using Glance to ask for help, the user's name, email, and phone are visible.email=user@example.comgives the user's emailphone=(111)222-3333gives the user's telephone number.
Parameters to the AgentJoin STU
You can add these optional parameters to the AgentJoin URL to control its operation.
viewersamewindow=1to start the session viewer in the same browser window that shows the session key prompt. If this parameter is not present, Glance opens a new window for the viewer.
These optional parameters control the prompt on the AgentJoin page. For more information, please contact Glance Customer Success.
mode=universaljoinmode=chatinvitationmode=smsinvitation
STUs with single sign-on
If your account uses SAML2.0 single sign-on, you use SSO-specific STUs. They require an identity provider identifier. This is the account's numeric Group ID at Glance.
These examples use a Group ID of EXAMPLE.
Replace EXAMPLE with your Glance Group ID or Partner ID.
Accessing any STU starts a service-provider-initiated sign-on (login) operation if the user is not yet signed on.
These STUs give direct access to sessions. When a Glance user visits one of these STUs, they immediately see the session page.
https://www.glance.net/agentjoin/AgentJoin.aspx?idpid=EXAMPLEprompts for a session key.https://www.glance.net/agentjoin/AgentView.aspx?idpid=EXAMPLE&SessionKey=kkkkis useful when you already know the session key. It joins the session directly. When using this STU the actual session key goes in place ofkkkk.
You may use the optional parameters mentioned earlier in this page with these STUs.
To start an interactive session on Glance's Account Management page, use this STU.
https://www.glance.net/account/GetLoginKey.aspx?sso=1&idpid=EXAMPLE&redirect=/account/AccountSummary.aspx
To obtain a Login Key for use by native client software, the STU is:
https://www.glance.net/account/GetLoginKey.aspx?sso=1&idpid=EXAMPLE
To show a SAML single sign-on troubleshooting page, use this STU. More information on troubleshooting single sign-on is here.
https://www.glance.net/account/GetLoginKey.aspx?sso=1&test=11&idpid=EXAMPLE
Alternative identifiers for your single sign-on account.
In place of idpid=EXAMPLE, you may use idpname=EXAMPLE. When this is done, Glance's service uses a name rather than a number to look up the group. Replace EXAMPLE with your account's group name, provided by Glance Customer Support.
In place of idpid=EXAMPLE, you may also use idptoken=TOKENVALUE. When this is done, Glance's service uses the value you place in the Unique Account Identifier field on SAML provisioning screen.
Replace TOKENVALUE with the name you put into that field.
This is suitable for such things as Salesforce Organization IDs and Azure tenant unique names.
In place of idpid=EXAMPLE it is also possible to provide idpusername=USER.glance.net.
When this is done, Glance's service uses the username provided to look up the account (Glance group).
This option is convenient in cases where the group name is not known but the username is.
Replace USER.glance.net with the Glance username (also known as the Glance Address) of a user (any user) in the account. If you are not sure what value to use, please contact Glance Customer Support.

